
Qabastech offers Artificial Intelligence powered Cyber Security Solutions. We integrate and deploy advanced technologies in artificial intelligence (AI) at all levels of cyber security for the benefit of customers.
Artificial intelligence has proven to have surpassed humans, in real life business challenges. Human thoughts and consciousness result in ability to perceive, observe, comprehend, understand, act and foresee. This combination of several functions exhibits intelligence in people, to manage day to day activities and survive


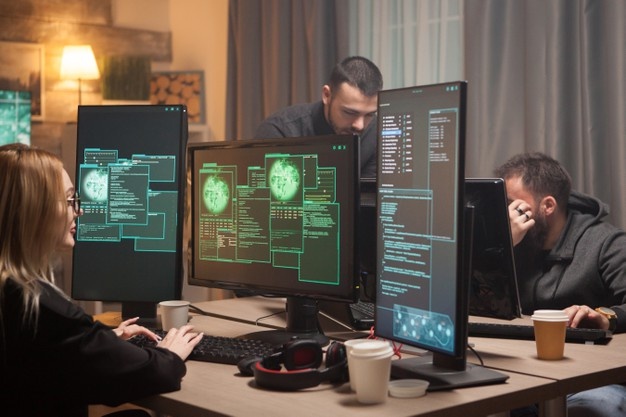
Artificial Intelligence emulates these capabilities in external world for the benefit for human progress. Cyber security solutions require specialists to meet dynamic tactics used by the adversaries. Cyber warriors can augment their skills with use of AI in cyber security solutions. The key driving forces for use of AI are speed of Impact and complexity of attack patterns, which are difficult to manage with conventional approaches.
AI in cyber security improves robustness, response and resilience. Enterprises in modern time require artificial intelligence to identify threats and respond to cyberattacks. Artificial Intelligence in cybersecurity enables organizations to detect, predict, monitor and facilitate automation of response against cyberthreats in real time. The capabilities of machines are expected to exceed that of a human security analyst and use of AI based products will be necessary to respond to cyberattacks

Qabastech Cyber Security Intelligence offers innovative solutions for enterprises to meet dynamic cyber risks landscape. Explosive digital transformations increase exposure for cyber-attacks. Cyber security readiness has become one of the major performance indicators of business resilience for digital transformation initiatives across Kingdom of Saudi Arabia. CIO’s in the kingdom see managing cyber security as the toughest challenge in the current and upcoming years
Cyber Security consultation and strategy
Cyber Threat Management Solutions
Managed Threat Detection and Response
Identity Access Management
Privilege Access Management
Vulnerability assessment and penetration testing
Support adherence to standards / compliance
SAMA Compliance